Everyone who wants to protect himself from intruders try to organize safe and anonymous access to web servers. Nowadays, almost all users can lose their personal data and “catch” a virus if they disclose their real email and IP-address. Even your provider can be your “enemy”, if he restricts your access to some websites and services, used by you for comfortable work and leisure.
Previously, the organization of safe and anonymous access to the internet could be performed only by data security professionals, who had a vast knowledge of network protocols and philosophy of networking. Besides that, users had to install additional software with complex configuration.
In recent years, this situation has changed as a lot of “one click” services for anonymous communication appeared in the internet. The easiest way is to use SOCKS-proxy and disposable mail to hide your activity from intruders and to get an access to websites and services, blocked by your provider.
What is SOCKS-proxy and how it works
Socks-proxy is a remote proxy server for transparent and anonymous data transfer from client to some server. In contrast to widely used http proxy, socks proxy enables you to use proxy server not only for browsers, but also for all software, installed on your device. For example, using socks proxy you can proxify your email clients, messengers, etc.
To establish socks proxy connection you need to get an access to SOCKS Proxy and to install and configure special software for forwarding traffic through socks server (for example, SocksCap, FreeCap, etc).
How to get an access to Socks Proxy
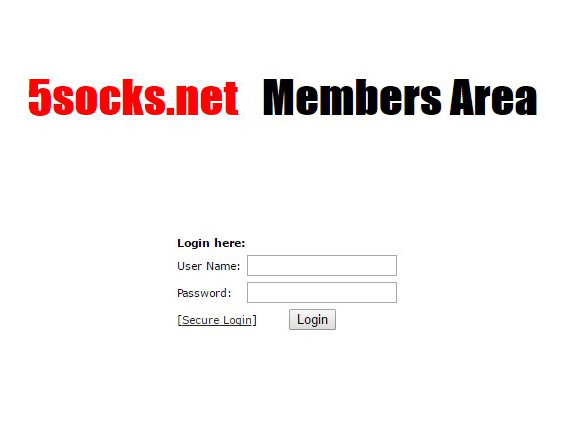
- Open https://admin.5socks.net/ and log into your account.
After logging in, you’ll get an access to your Administration Panel, where you can search available socks 4/5 proxy by different parameters (Proxy Search), choose any available proxy from list (List Proxies) or manage your account details (Account Settings).
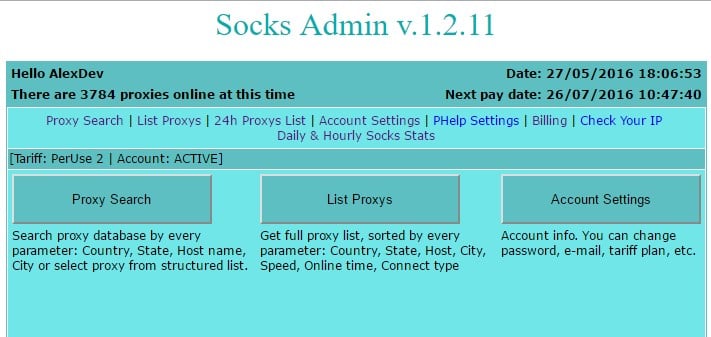
- Click Proxy Search button and choose the country where the proxy servers you want to use are located. Click Go to continue.
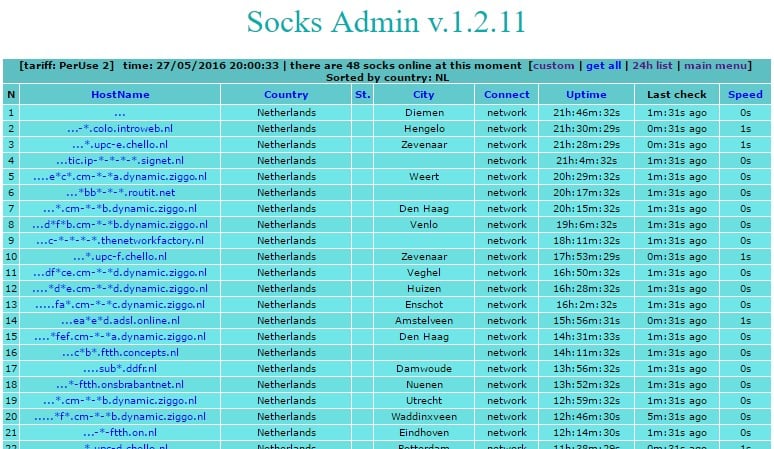
You’ll see the results with detailed information about all available proxy servers.
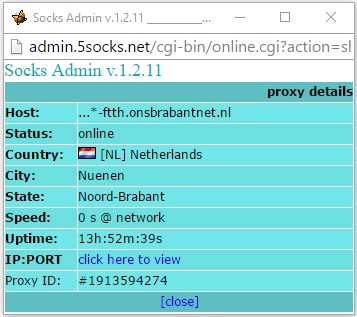
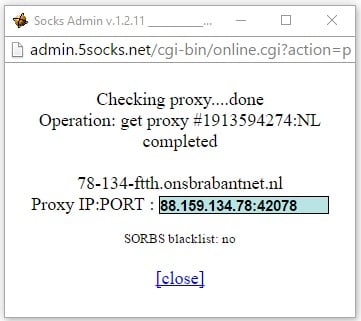
Click on the server name to view detailed information about proxy server. Press Click here to view to see an IP address of that proxy server.
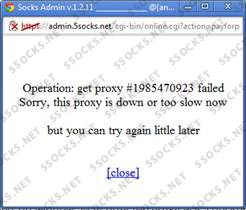
- Wait a few seconds while the software connects to server. Next, you’ll see an information about IP address and port of the proxy server. Copy this information. In this example, the IP address is 83.85.214.142, port 58933.
Configuring Firefox for using SOCKS proxy server
In most cases, it’s enough to configure only web browser without installing any additional software.
- Launch Firefox, open setup panel and go to «Options». Open tab «Advanced», then «Network» and press «Settings» button.


- Enter this parameters:
-
Manual proxy configuration;
-
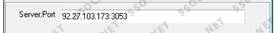
SOCKS v5. Enter IP address of the socks proxy server from https://5socks.net (in this example - 83.85.214.142);
-
Enter port number (in this example - 58933);
-
Activate “SOCKS5” and “Remote DNS”;
-
Click «ОК».
-
Done.
-
Check your IP-address at http://www.ipleak.com/.

As we see, Firefox works through socks proxy, and the IP-address of your computer is 83.85.214.142 (Netherlands).
How to use disposable mail?
You needn’t perform any registration process to use disposable mail – just open www.temp-mail.org to get an access to the control panel of your disposable mailbox. Your temporary email address is displayed at the top of the page (in this example - [email protected]).

Control buttons:
Press “Copy” button to copy an address of your mailbox into clipboard.
Click on “Refresh” button to view incoming mails.
“Change” button allows user to input any desirable email address for temporary mailbox.
Press “Delete” button to delete current temporary mailbox and to create new temporary mailbox.
Your disposable mailbox remains valid even if you close your browser and restart computer. Just open again www.temp-mail.org to get an access to your last disposable mailbox.
Incoming messages are valid for 60 minutes, then it’ll be deleted.
What is the result?
Using socks proxy and disposable email to hide IP address and real mail enables users to get an anonymous and safe access to all web services even if they are blocked by your provider. It guarantees you protection from intruders, who are unable to monitor your web actions.
 5socks.net
5socks.net